

Oracle Virtual Directory (OVD) can function as a policy store. A single directory server instance can function as a:
Using a single directory server simplifies administration tasks. This scenario describes how to configure a single directory server instance to store policy data and encryption keys.
Note: If your implementation requires, you can configure a separate key store.
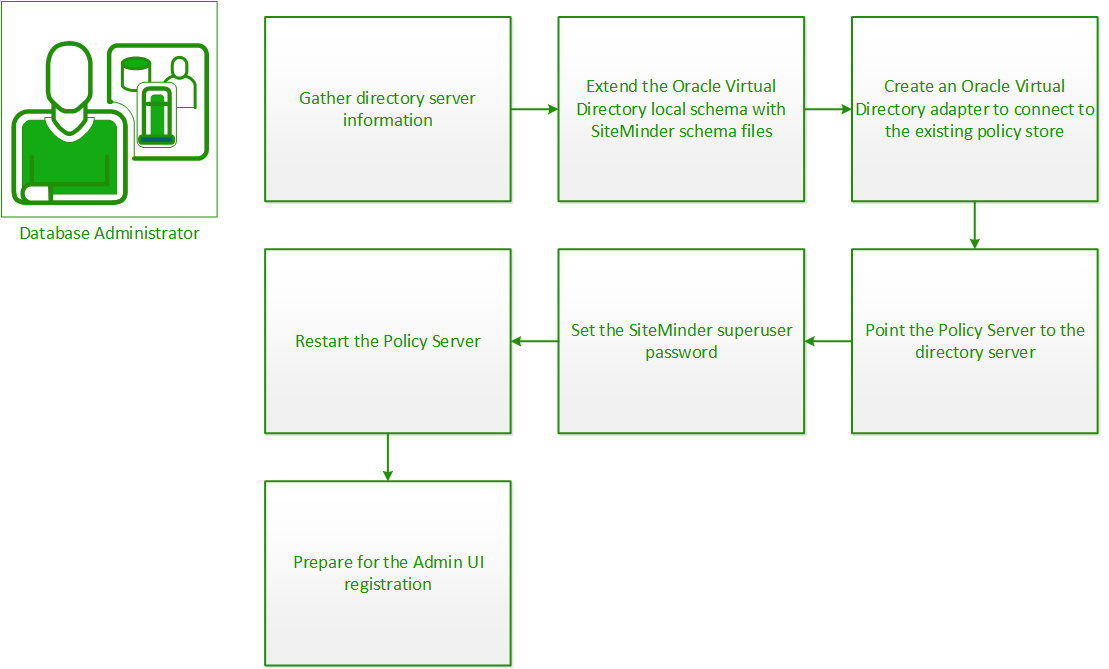
To configure Oracle Virtual Directory as a policy store, do the following procedures:
Configuring an LDAP directory server as a policy store or upgrading an existing policy store requires specific directory server information. Gather the following information before beginning. You can use the Policy Store Worksheets to record your values.
Note: Policy and data store worksheets are provided to help you gather and record information before configuring or upgrading a CA SiteMinder® data store. You can print the applicable worksheet and can use it to record required information before beginning.
Specifies the fully-qualified host name or the IP Address of the directory server.
(Optional) Specifies a non-standard port.
Default values: 636 (SSL) and 389 (non-SSL)
Specifies the LDAP user name of a user who has privileges to create, read, modify, and delete objects in the LDAP tree underneath the policy store root object.
Specifies the password for the Administrative DN.
Specifies the distinguished name of the node in the LDAP tree where policy store objects are to be defined.
Specifies the pathname of the directory where the SSL client certificate database file resides.
Limit: SSL only
Extend the Oracle Virtual Directory with the following CA SiteMinder® schema files:
Follow these steps:
ovd_sm_schema.ldif
ovd_xps_schema.ldif
ldapmodify -h OVD_Host -p OVD_Port -D cn=Admin -w Admin_Password -v -a -f ovd_sm_schema.ldif
ldapmodify -h OVD_Host -p OVD_Port -D cn=Admin -w Admin_Password -v -a -f ovd_xps_schema.ldif
dsconf reindex -h localhost -p OVD_Port -e "ou=Netegrity,root_database"
Specifies the OVD system IP Address or fully qualified domain name.
Specifies the port on which the OVD instance is running.
Specifies the OVD server admin with rights to modify the schema.
Specifies the server admin password.
To create an Oracle Virtual Directory LDAP adapter to connect to your existing policy store, use the Oracle Directory Services Manager.
Follow these steps:
Select LDAP.
Enter a unique name for the LDAP adapter.
Select an adapter template that corresponds to the directory type of the existing policy store.
Select No.
Enter the hostname or IP address of the remote host.
Enter the port at which the remote host instance is running.
Enter the credentials of a directory user who has permission to modify directory contents.
Password for the user that is specified in the Secure proxy Bind DN field.
Click Browse and select the DN at which the policy data is stored.
Enter a local DN at which to map the policy data.
You point the Policy Server to the policy store so the Policy Server can access the policy store.
Follow these steps:
Important! If you are accessing this graphical user interface on Windows Server 2008, open the shortcut with Administrator permissions. Use Administrator permissions even if you are logged in to the system as an Administrator. For more information, see the release notes for your CA SiteMinder® component.
Policy Store
LDAP
Note: You can click Help for a description of fields, controls, and their respective requirements.
The default CA SiteMinder® administrator account is named:
siteminder
The account has maximum permissions.
We recommend that you do not use the default superuser for day–to–day operations. Use the default superuser to:
Follow these steps:
Specifies the Policy Server installation path.
Note: The utility is at the top level of the Policy Server installation kit.
smreg -su password
Specifies the password for the default CA SiteMinder® administrator.
Limits:
Note: If you are configuring an Oracle policy store, the password is case–sensitive. The password is not case–sensitive for all other policy stores.
The password for the default CA SiteMinder® administrator account is set.
Enable the advanced authentication server as part of configuring your Policy Server.
Follow these steps:
The master key screen appears.
Note: If you are installing another (nth) Policy Server, use the same encryption key for the Advanced Authentication server that you used previously.
The advanced authentication server is enabled.
You restart the Policy Server for certain settings to take effect.
Follow these steps:
The Policy Server stops as indicated by the red stoplight.
The Policy Server starts as indicated by the green stoplight.
Note: On UNIX or Linux operating environments, you can also execute the stop-all command followed by the start-all command to restart the Policy Server. These commands provide an alternative to the Policy Server Management Console.
You use the default CA SiteMinder® super user account (siteminder) to log into the Administrative UI for the first–time. The initial login requires that you to register the Administrative UI with a Policy Server, which creates a trusted relationship between both components.
You prepare for the registration by using the XPSRegClient utility to supply the super user account name and password. The Policy Server uses these credentials to verify that the registration request is valid and that the trusted relationship can be established.
Consider the following:
To prepare for the Administrative UI registration
XPSRegClient siteminder[:passphrase] -adminui-setup -t timeout -r retries -c comment -cp -l log_path -e error_path -vT -vI -vW -vE -vF
Specifies the password for the default CA SiteMinder® super user account (siteminder).
Note: If you do not specify the passphrase, XPSRegClient prompts you to enter and confirm one.
Specifies that the Administrative UI is being registered with a Policy Server for the first–time.
(Optional) Specifies the allotted time from when you to install the Administrative UI to the time you log in and create a trusted relationship with a Policy Server. The Policy Server denies the registration request when the timeout value is exceeded.
Unit of measurement: minutes
Default: 240 (4 hours)
Minimum Limit: 15
Maximum Limit: 1440 (24 hours)
(Optional) Specifies how many failed attempts are allowed when you are registering the Administrative UI. A failed attempt can result from submitting incorrect CA SiteMinder® administrator credentials when logging into the Administrative UI for the first–time
Default: 1
Maximum Limit: 5
(Optional) Inserts the specified comments into the registration log file for informational purposes.
Note: Surround comments with quotes.
(Optional) Specifies that registration log file can contain multiple lines of comments. The utility prompts for multiple lines of comments and inserts the specified comments into the registration log file for informational purposes.
Note: Surround comments with quotes.
(Optional) Specifies where the registration log file must be exported.
Default: siteminder_home\log
siteminder_home
Specifies the Policy Server installation path.
(Optional) Sends exceptions to the specified path.
Default: stderr
(Optional) Sets the verbosity level to TRACE.
(Optional) Sets the verbosity level to INFO.
(Optional) Sets the verbosity level to WARNING.
(Optional) Sets the verbosity level to ERROR.
(Optional) Sets the verbosity level to FATAL.
XPSRegClient supplies the Policy Server with the administrator credentials. The Policy Server uses these credentials to verify the registration request when you log into the Administrative UI for the first–time.
|
Copyright © 2013 CA.
All rights reserved.
|
|