

To configure CA SiteMinder® Web Services Security to produce WS-Security headers, create a response and associate it with resources in a web service security policy. This response data is used by the SiteMinder WSS Agent to generate WS‑Security headers. The SiteMinder WSS Agent then inserts these headers into the SOAP message header and delivers them to the protected web service.
Use variable types, if needed, to pass data back to the web service. Variables are resolved by the Policy Server at run time, when it generates the response.
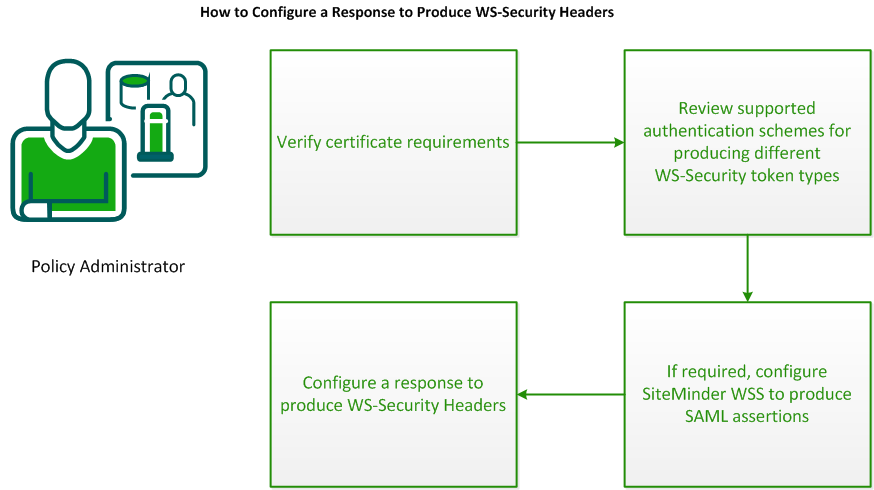
To configure responses to produce WS-Security Headers for outgoing messages, do the following procedures:
Before you configure a response to produce WS‑Security headers, verify that the following requirements are met:
You can configure responses to produce any type of WS-Security token upon successful authorization of a request. However, not every authentication scheme gathers all the necessary information (username, clear text password, SOAP message) from an incoming request to create every type of token.
If a response is configured to create a token that requires anything that the configured authentication scheme does not provide, header creation fails. Verify that the authentication method that you plan to use is suitable to produce the WS-Security token that you want to produce in response.
The following table shows which WS-Security tokens can be produced for each authentication method.
|
|
|
WS-Security Token Types That Can be Produced |
|||
|---|---|---|---|---|---|
|
Authentication Method |
|
Username and Password |
Username and Password Digest |
SAML |
X.509 |
|
Basic (SiteMinder WSS Agent for Web Servers only) |
|
No |
Yes |
No |
No |
|
XML-DCC |
|
Yes |
Yes |
Yes |
Yes |
|
XML-DSIG |
|
No |
No |
Yes |
Yes |
|
SAML Session Ticket |
|
No |
No |
Yes |
Yes |
|
WS-Security Username and Password Token |
|
Yes |
Yes |
Yes |
Yes |
|
WS-Security Username and Password Digest Token |
|
No |
Yes |
Yes |
Yes |
|
WS-Security SAML Token |
|
No |
No |
Yes |
Yes |
|
WS-Security X.509 Token |
|
No |
No |
Yes |
Yes |
|
SiteMinder Session (SMSESSION) Cookie |
|
No |
No |
No |
No |
If you are configuring CA SiteMinder® Web Services Security to add WS-Security headers containing SAML assertions tokens to outgoing messages, you must first perform some additional configuration in the Administrative UI
In all SAML token generation situations, you must create an Affiliate domain. Additionally, you must perform the following steps depending on the version of SAML tokens you need to generate:
Note: Affiliate domains and related SAML token functionality are implemented as part of CA SiteMinder® Federation Security Services on the Policy Server. For more information, see Federation Manager Guide: Legacy Federation and Federation Manager Guide: Partnership Federation.
If you are configuring CA SiteMinder® Web Services Security to add WS-Security tokens containing SAML 1.x assertions to SOAP documents for consumption by other web services, you must configure the SAML Assertion Generator to produce the SAML 1.1 assertions that will be used in those tokens.
Note: The SAML Assertion Generator is a component of CA SiteMinder Federation Security Services on the Policy Server. For more information, see the CA SiteMinder Federation Security Services Guide.
The SAML Assertion Generator uses static configuration data from two sources to determine how to construct assertions:
Specifies domain-wide SAML assertion generation parameters
Define a set of parameters for the SAML Assertion Generator
Once configured, the SAML Assertion Generator is triggered to generate an assertion when a WS-Security SAML response (which specifies the affiliate to use to generate the assertion and dynamic information about how the assertion and message should be signed) is triggered by an authorizing policy.
Configure the AMAssertionGenerator.properties File
The AMAssertionGenerator.properties file contains domain-wide configuration parameters required for generating SAML assertions.
To configure the AMAssertionGenerator.properties file for CA SiteMinder® Web Services Security
Specifies the URL of the authentication web service that is issuing the assertion. Must match the Issuer DN in the enterprise certificate. This value is used for unsigned assertions. For example:
AssertionIssuerID = http://www.acmewidget.com/ordering
Specifies the domain name of the enterprise issuing the assertion. For example:
SecurityDomain = www.example.com
Not used by CA SiteMinder® Web Services Security.
Configure Affiliate Domains and Affiliate Objects
You require an affiliate domain containing and affiliate object to configure the SAML Assertion Generator produce SAML 1.x assertions in WS-Security SAML tokens.
To configure affiliate domains and affiliate objects, follow the associated procedures in Federation Manager Guide: Legacy Federation. However, because CA SiteMinder® Web Services Security does not use the affiliate object to define an affiliate organization, you do not need to specify all the options.
Note: Affiliate objects configured for CA SiteMinder® Web Services Security do not define the affiliate organization for which the assertion is intended. Assertions generated for CA SiteMinder® Web Services Security can be sent to any web service protected by the WS-Security authentication scheme (or similarly capable third-party security application).
The following list summarizes the affiliate configuration parameters that CA SiteMinder® Web Services Security uses to generate WS-Security SAML tokens. The wizard may require you to enter values for other parameters, but these are not used by CA SiteMinder® Web Services Security.
General page
Specifies the name of the affiliate object (must be unique across all affiliate domains).
This name is referenced by WS-Security policy responses (by defining a txm_wssec_saml_affiliate attribute whose value matches the name of the affiliate object).
Activates the affiliate object.
This option must be set for CA SiteMinder® Web Services Security to produce SAML 1.x assertions.
(Optional) Specifies times when assertion can be issued.
(Optional) Specifies IP addresses that are allowed to generate SAML assertions.
User page
Specifies the users and groups (from the user directory or directories defined in the affiliate domain) for whom assertions should be generated.
Assertions page
(Optional) Specifies the URI of a document that describes the terms and conditions of the agreement between the token issuer and consumer. This value is added to the assertion and can be used for authentication purposes. (If a request’s assertion token contains an audience value, that value must match one specified in the WS-Security scheme for the request to be authenticated.)
Additionally, the web service can parse the actual audience document to obtain additional information.
(Optional) Specifies the amount of time, in seconds, that the assertion will be valid.
(Optional) Specifies the difference, in seconds, between the system clock time of the SAML assertion producer and the system clock time of the SAML assertion consumer.
Not used by CA SiteMinder® Web Services Security (leave option unset).
(Optional) If specified, an attribute statement will be included in the assertion that can be used for use in authentication and authorization decisions.
SAML Service Provider objects define parameters used by the SAML Assertion Generator to produce SAML 2.0 assertions for use in WS-Security SAML tokens.
Note: When you configure a service provider object for use by CA SiteMinder® Web Services Security, you are not defining a service provider organization for which the assertion is intended. Assertions generated for CA SiteMinder® Web Services Security can be sent to any web service protected by the WS-Security authentication scheme (or similarly capable third-party security application).
To configure SAML Service Provider objects, generally follow the associated procedures in the CA SiteMinder Federation Security Services Guide. However, because CA SiteMinder® Web Services Security does not use the affiliate object to define a service provider organization, you do not need to specify all the options. Fields whose use is different for use by CA SiteMinder® Web Services Security are described below.
Specifies the name of the service provider object (must be unique across all affiliate domains). This name is referenced by WS-Security policy responses (by defining a txm_wssec_saml_affiliate attribute whose value matches the name of the affiliate object).
Sets the Enabled check box to activate the service provider object. This option must be set for CA SiteMinder® Web Services Security to produce SAML 2.0 assertions.
Not used by CA SiteMinder® Web Services Security. However, a valid value is required. CA recommends using "http:\\localhost\"
Not used by CA SiteMinder® Web Services Security.
Choose the HTTP-Post option.
To define the properties of WS-Security headers you want CA SiteMinder® Web Services Security to produce, create a WS-Security header response in an application security policy.
Note: If you are using the domain security model, create a WS-Security header response in the web service domain.
Follow these steps:
The Create Application Response pane opens.
Note:
The fields on the Attribute Fields group box are updated to match the specified attribute type.
The Create Response Attribute Task is submitted for processing, and the response attribute is added to the Attribute List on the Create Response Attribute pane.
The Create Response Task is submitted for processing and you are returned to the Responses tab.
Note:
The TXM_WSSEC_TOKEN_TYPE variable name/value pair determines the WS‑Security token type to generate. A response attribute that defines TXM_WSSEC_TOKEN_TYPE is required in all WS-Security header responses.
Specifies the type of WS‑Security token the SiteMinder WSS Agent should create and add to the WS‑Security header for message authentication:
Attribute kind: Static
Variable value: One of the following:
The following table describes the response variable name/value pairs for generating username and password (digest or clear text) and X.509 certificate tokens in WS-Security headers. That is, if the TXM_WSSEC_TOKEN_TYPE response attribute variable is set to password, password_nodigest, or X509.
|
Variable Name |
Variable Value |
Attribute Type |
Meaning |
|---|---|---|---|
|
TXM_WSSEC_USER_PASSWORD (Required)
|
userpassword (Value most common for LDAP user directories -- if you have used a custom naming scheme for your LDAP directory, the value will be different.) |
User Attribute |
Specifies the LDAP query string that the SiteMinder WSS Agent uses to retrieve the web service consumer’s password from the user store. This value is then placed in the token. |
|
Or password |
Static |
Specifies a static password value to be used in the token. |
|
|
TXM_WSSEC_ROLE (Optional) |
token_role_name |
Static |
Specifies the value of a SOAP role attribute that identifies the WS‑Security header element containing the Username and Password or X.509 token. |
|
TXM_WSSEC_TIMESTAMP (optional) |
|
Static |
If True, tells the agent to add a wsu:Timestamp element to the WS‑Security SOAP header that specifies the time that the message was created |
|
TXM_WSSEC_TIMESTAMP _EXPIRY (Valid only if TXM_WSSEC_TIMESTAMP is True) |
message lifespan in seconds |
Static |
Tells the agent to add a wsu:Expires element to the wsu:Timestamp element in the WS‑Security SOAP header. The value of the wsu:Expires element is an absolute time based on the time of message creation and the specified message lifespan. |
|
TXM_WSSEC_SIGNATURE (optional) |
|
Static |
For WS‑Security tokens of type password or X509, tells the agent to retrieve the enterprise private key from the certificate data store (CDS) and use it to digitally sign all or part of the SOAP document:
By default, tokens are signed using RSA-SHA1. |
|
TXM_WSSEC_SIGNATURE_ALG (Valid only if TXM_WSSEC_SIGNATURE is set) |
|
Static |
|
The following table describes the response attribute variable name/value pairs for generating SAML tokens in WS-Security headers. That is, if the TXM_WSSEC_TOKEN_TYPE response attribute variable is set to SAML.
|
Variable Name |
Variable Value |
Attribute Type |
Meaning |
|---|---|---|---|
|
TXM_WSSEC_SAML20_ASSERTION (Required for SAML 2.0) |
|
Static |
Specifies whether the generated SAML assertion token is SAML 2.0 compliant. |
|
TXM_WSSEC_SAML20_SPID (required for SAML 2.0) |
SAML_20_audience_value |
Static |
Specifies the value of the <saml:Audience> element in a generated SAML 2.0 assertion token. |
|
TXM_WSSEC_SAML_AFFILIATE (Required) |
affiliate_or_service_provider_object_name |
Static |
Identifies the affiliate (SAML 1.x) or service provider (SAML 2.0) object that configures how SAML assertions will be produced for inclusion in SAML tokens. |
|
TXM_WSSEC_ (optional) |
SAML_assertion_token_role_name |
Static |
Specifies the value of a SOAP role attribute that identifies the WS-Security header element containing the SAML assertion token. |
|
TXM_WSSEC_SAML_SIG_REQUIRED |
|
Static |
Specifies how the assertion and document should be signed:
Any other value or no value results in the default—an assertion with a bearer confirmation method. |
|
TXM_WSSEC_ (Required for holder-of-key signing) |
|
Static |
If TXM_WSSEC_SAML_SIG_REQUIRED is set to HK, this value specifies where CA SiteMinder® Web Services Security should obtain the web service consumer’s public key:
|
|
TXM_WSSEC_ (Required if web service consumer public key is obtained from a user store for signing) |
usercertificate This value is the most common for LDAP user directories. If you have used a custom naming scheme for your LDAP directory, the value will be different. |
User Attribute |
If TXM_WSSEC_SAML_USER_ Note: CA SiteMinder® Web Services Security automatically completes the query string using the value you specify. |
|
TXM_WSSEC_ (optional) |
|
Static |
A value of True causes a timestamp to be generated for use in SAML assertions. Note: If TXM_WSSEC_SAML_SIG |
|
TXM_WSSEC_ (optional) |
message _lifespan_in_seconds |
Static |
Tells the agent to add an expiry element to the timestamp used in SAML assertions. The value of this expiry element is an absolute time based on the time of assertion creation and the specified message lifespan. |
The following table describes response attribute variable name/value pairs that can be configured to tell the SiteMinder WSS Agent to encrypt message elements or to pass a decrypted version of a message to the recipient web service.
Note: There are two versions of each XML encryption-related name/value pair—use the former for use with messages with username/password or X.509 tokens, use the latter for use with messages with SAML tokens.
|
Variable Name |
Variable Value |
Attribute Type |
Meaning |
|---|---|---|---|
|
TXM_WSSEC_ENCRYPT_PUB_KEY_ROLE or TXM_WSSEC_SAML_ENCRYPT_PUB_KEY_ROLE (required) |
name_of_WS‑Security_token_consumer |
Static |
Specifies the value of a SOAP role attribute that identifies the WS‑Security header element containing the recipient's X.509 certificate. The public key in this certificate is used to encrypt the symmetric key. The corresponding private key must be held by the intended message recipient. This element is required. If no role is specified, the variable must be declared with a null value; CA SiteMinder® Web Services Security will then obtain the key in the WS‑Security header with no role, of which only one is allowed. |
|
TXM_WSSEC_ENCRYPT_ DECRYPT or TXM_WSSEC_SAML_ENCR YPT_DECRYPT |
|
Static |
Specifies whether the SiteMinder WSS Agent should pass an incoming encrypted message to the web service in its encrypted or decrypted form. If True, the SiteMinder WSS Agent will replace the current message with the decrypted version of the message, if available. |
|
TXM_WSSEC_ENCRYPT_ ELEMENT or TXM_WS SEC_SAML_ENCRYPT_ELEMENT |
|
Static |
Identifies the message element to be encrypted. You should add one such name value/pair for each element you want encrypted. For example, configure one name/value pair for the message body and one name/value pair for the token. For TXM_WSSEC_ENCRYPT_ If UsernameToken, Username and Password and Username and Password Digest tokens will be encrypted. If Body, the message body will be encrypted. For TXM_WSSEC_SAML_ If Assertion, SAML assertion token will be encrypted. If Body, the message body will be encrypted. |
|
TXM_WSSEC_ENCRYPT_ OR_SIGN_FIRST or TXM_WSSEC_SAML_ ENCRYPT_OR_SIGN_FIRST |
|
Static |
Indicates whether encryption or signing should be performed first. |
|
TXM_WSSEC_ENCRYPT_ ALG_KEY or TXM_WSSEC_SAML_ENC RYPT_ALG_KEY |
|
Static |
Indicates the encryption algorithm to use to encrypt the symmetric encryption key. |
|
TXM_WSS EC_ENCRYPT_ALG_DATA or TXM_WSSEC_SAML_ENC RYPT_ALG_DATA |
|
Static |
Indicates the encryption algorithm to use to encrypt the data element or elements that have been specified using TXM_WSSEC_ENCRYPT[_SAML] |
The following table describes response attribute variable name/value pairs that can be configured to tell the SiteMinder WSS Agent how to handle the mustUnderstand attribute in WS‑Security request , or to remove the mustUnderstand or the entire security token from messages passed to the recipient web service.
|
Variable Name |
Variable Value |
Attribute Type |
Meaning |
|---|---|---|---|
|
TXM_WSSEC_MUST_UNDERSTAND (optional) |
|
Static |
Determines how the SiteMinder WSS Agent behaves with respect to the mustUnderstand attribute when consuming and producing messages. For specifics of the behavior of this variable when consuming and producing headers, see TXM_WSSEC_MUST_UNDERSTAND Response Variable Effect Detail. |
|
TXM_WSSEC_REMOVE (optional) |
|
Static |
Determines whether the SiteMinder WSS Agent removes WS-Security headers from messages.
|
TXM_WSSEC_MUST_UNDERSTAND Response Variable Effect Detail
The following table describes the exact behavior of the SiteMinder WSS Agent when consuming and producing WS‑Security tokens with different values of the TXM_WSSEC_MUST_UNDERSTAND response variable name/value pair.
|
TXM_WSSEC_MUST_UNDERSTAND Value |
Behavior when Consuming WS‑Security Tokens |
Behavior when Producing WS‑Security Tokens |
|---|---|---|
|
Not set |
If present in the WS‑Security header, leaves mustUnderstand="1". |
Places mustUnderstand="1" in the generated WS‑Security header |
|
False |
If present in the WS‑Security header, removes mustUnderstand="1" |
Does not place mustUnderstand="1" in the generated WS‑Security header |
|
True |
If present in the WS‑Security header, leaves mustUnderstand="1". |
Places mustUnderstand="1" in the generated WS‑Security header |
The following examples show how you can use WS‑Security responses.
This example shows how to create a response that generates a Username and Password Digest token and uses the enterprise private key to digitally sign the message’s SOAP envelope.
The following table shows the response attributes you must add to the response (all attributes are of type WebAgent-WS‑Security-Token):
|
Variable Name |
Variable Value |
Attribute Type |
|---|---|---|
|
TXM_WSSEC_TOKEN_TYPE |
password |
Static |
|
TXM_WSSEC_USER_PASSWORD |
userpassword |
User Attribute |
|
TXM_WSSEC_SIGNATURE |
all |
Static |
This example shows how to create a response that generates an X509v3 token and uses the enterprise private key to digitally sign the message’s SOAP envelope.
The following table shows the response attributes you must add to the response (all attributes are of type WebAgent-WS‑Security-Token):
|
Variable Name |
Variable Value |
Attribute Type |
|---|---|---|
|
TXM_WSSEC_TOKEN_TYPE |
X509 |
Static |
This example shows how to create a response that generates a SAML assertion token using the holder-of-key subject confirmation method, retrieving the subject’s public key from an associated user store.
The following table shows the response attributes you must add to the response (all attributes are of type WebAgent-WS‑Security-Token):
|
Variable Name |
Variable Value |
Attribute Type |
|---|---|---|
|
TXM_WSSEC_TOKEN_TYPE |
SAML |
Static |
|
TXM_WSSEC_SAML_AFFILIATE |
affiliate1 |
Static |
|
TXM_WSSEC_SAML_SIG |
hk |
Static |
|
TXM_WSSEC_SAML_USER_CERT_SRC |
User_Store |
Static |
|
TXM_WSSEC_SAML_USER_CERT |
usercertificate |
User attribute |
This example shows how to create a response that encrypts an incoming document and deliver the encrypted document to the web service.
The response generates a SAML assertion token using the sender vouches subject confirmation method and encrypts the SAML assertion and message body. The token and other related information are placed in a WS‑Security header identified by the SOAP actor/role samlrole.
The SAML assertion and the message body are encrypted using the public key certificate found in the WS‑Security header with the role pubkeyrole. The rsa-1_5 algorithm should be used to encrypt the symmetric encryption key; the tripledes-cbc algorithm should be used to encrypt the assertion and body data.
The document should be signed before encryption; the document and assertion should also be signed with a sender-vouches signature.
The following table shows the response attributes you must add to the response (all attributes are of type WebAgent-WS‑Security-Token):
|
Variable Name |
Variable Value |
Attribute Type |
|---|---|---|
|
TXM_WSSEC_TOKEN_TYPE |
SAML |
Static |
|
TXM_WSSEC_SAML_AFFILIATE |
affiliate2 |
Static |
|
TXM_WSSEC_SAML_ROLE |
samlrole |
Static |
|
TXM_WSSEC_SAML_SIG |
sv |
Static |
|
TXM_WSSEC_SAML_ENCRYPT_PUB_KEY_ROLE |
pubkeyrole |
Static |
|
TXM_WSSEC_SAML_ENCRYPT_ALG_KEY |
rsa-1_5 |
Static |
|
TXM_WSSEC_SAML_ENCRYPT_ALG_DATA |
tripledes-cbc |
Static |
|
TXM_WSSEC_SAML_ENCRYPT_ELEMENT |
Assertion |
Static |
|
TXM_WSSEC_SAML_ENCRYPT_ELEMENT |
Body |
Static |
|
TXM_WSSEC_SAML_ENCRYPT_OR_SIGN_FIRST |
sign |
Static |
This example shows how to create a response that decrypts an incoming encrypted message and passes it to the associated web service in a message with a SAML assertion token.
|
Variable Name |
Variable Value |
Attribute Type |
|---|---|---|
|
TXM_WSSEC_TOKEN_TYPE |
SAML |
Static |
|
TXM_WSSEC_SAML_AFFILIATE |
affiliate2 |
Static |
|
TXM_WSSEC_SAML_ENCRYPT |
yes |
Static |
|
Copyright © 2013 CA.
All rights reserved.
|
|